Explaining the widespread shift in tactics, techniques and procedures (TTPs) towards networks of compromised infrastructure, and how to defend against it.
Executive summary
What is the threat?
- China-nexus cyber actors have moved from using individually procured infrastructure to operating large scale “covert networks” – botnets built from compromised routers, and other edge devices.
- These networks are used for each phase of the Cyber Kill Chain, from reconnaissance and malware delivery, to command and control and data exfiltration against targets of espionage and offensive cyber operations.
- The threat is a dynamic, low-cost, deniable infrastructure model that can be rapidly re-shaped, rendering traditional static IP block lists ineffective.
What is the impact on affected organisations?
- Covert networks enable China-nexus actors to launch cyber attacks against UK organisations, stealing sensitive data and potentially disrupting critical services.
- Because the covert networks are constantly refreshed and share nodes across multiple threat groups, defenders face “IOC extinction” – indicators of compromise disappear as quickly as they are discovered.
- Consequently, organisations that rely solely on static defences risk being bypassed, while those that adopt adaptive, intelligence driven measures can better mitigate the risk.
What should I do?
- The NCSC and the Cyber League, in conjunction with the co-sealing agencies, have developed advice specifically to combat this threat.
- The advisory contains guidance for small, medium, and large organisations.
- All organisations should map and baseline their edge device traffic, especially VPN and remote access connections, and adopt dynamic threat feed filtering that includes known covert network indicators.
- Potential victims should implement two-factor authentication for remote access and, where possible, apply zero trust controls, IP allow lists, and machine certificate verification.
- Larger or high-risk entities should consider active hunting of suspicious SOHO/IOT traffic, geographic profiling, and machine learning based anomaly detection.
Co-sealers
With support from the UK Cyber League, this advisory has been jointly released by the National Cyber Security Centre (NCSC-UK) and international partners:
- Australian Signals Directorate’s (ASD’s) Australian Cyber Security Centre (ACSC)
- Communications Security Establishment Canada’s (CSE’s) Canadian Centre for Cyber Security (Cyber Centre)
- Germany Federal Office for the Protection of the Constitution - Bundesamt für Verfassungsschutz (BfV)
- Germany Federal Intelligence Service – Bundesnachrichtendienst (BND)
- Germany Federal Office for Information Security - Bundesamt für Sicherheit in der Informationstechnik (BSI)
- Japan National Cybersecurity Office (NCO) - 国家サイバー統括室
- Netherlands General Intelligence and Security Service - Algemene Inlichtingen- en Veiligheidsdienst (AIVD)
- Netherlands Defence Intelligence and Security Service - Militaire Inlichtingen- en Veiligheidsdienst (MIVD)
- New Zealand National Cyber Security Centre (NCSC-NZ)
- Spain National Cryptologic Centre – Centro Criptológico Nacional (CCN)
- Sweden National Cyber Security Centre - Nationellt cybersäkerhetscenter (NCSC-SE)
- United States Cybersecurity and Infrastructure Security Agency (CISA)
- United States Department of Defense Cyber Crime Center (DC3)
- United States Federal Bureau of Investigation (FBI)
- United States National Security Agency (NSA)
Its purpose is to provide network defenders with the tools needed to defend against China-nexus cyber actors and their tactic of using large scale networks of compromised devices (covert networks) to route their cyber activity.
Introduction
Over the past few years there has been a major shift in the tactics, techniques and procedures (TTPs) used by China-nexus cyber actors, moving away from the use of individually procured infrastructure, and towards the use of externally provisioned, large-scale networks of compromised devices.
The NCSC believes that the majority of China-nexus threat actors are using these networks (hereafter “covert networks”), that multiple covert networks have been created and are being constantly updated, and that a single covert network could be being used by multiple actors. These networks are mainly made up of compromised Small Office Home Office (SOHO) routers, as well as Internet of Things (IoT) and smart devices.
Anyone who is a target of China-nexus cyber actors may be impacted by the use of covert networks. They have been used by Chinese state-sponsored actors Volt Typhoon to pre-position offensive cyber capabilities on critical national infrastructure. The group Flax Typhoon used a different covert network of compromised infrastructure to conduct cyber espionage.
The use of covert networks of compromised devices - also known as botnets - to facilitate malicious cyber activity is not new, but China-nexus cyber actors are now using them strategically, and at scale.
This advisory describes the typical makeup of a covert network and what they are being used for. It also includes protective advice for organisations being targeted by cyber activity using a covert network as an access vector.
Covert networks
Covert networks are used to connect across the internet in a low-cost, low-risk, deniable way, disguising the origin and attribution of malicious activity. Actors have been observed using them for each phase of their Cyber Kill Chains, from performing scans as part of reconnaissance, to the delivery of malware, communicating with said malware, and exfiltrating stolen data from a victim. They can also be used for general deniable internet browsing, allowing threat actors to research exploitation techniques, new TTPs, and their victims without attribution. Some covert networks are also used by legitimate customers to browse the internet, making it challenging to attribute malicious activity.
There is evidence that covert networks used by China-nexus actors are created and maintained by Chinese information security companies. A network known to network defenders as Raptor Train, which in 2024 infected more than 200,000 devices worldwide, was controlled and managed by the Chinese company, Integrity Technology Group. This company was also assessed by the FBI to be responsible for the computer intrusion activities attributed to China-based hackers known as Flax Typhoon.
“Botnet operations represent a significant threat to the UK by exploiting vulnerabilities in everyday internet-connected devices with the potential to carry out large-scale cyber attacks” – NCSC Director of Operations, Paul Chichester
Covert networks mostly consist of compromised SOHO routers, but they also pull in any vulnerable device they can exploit at scale. Raptor Train was made up of thousands of SOHO routers and IoT devices, such as web cameras and video recorders, as well as firewalls and Network Attached Storage (NAS) devices. The KV Botnet used by Volt Typhoon was mainly made up of vulnerable Cisco and NetGear routers. The edge devices were vulnerable because they were “end of life” – out of date and no longer receiving updates or security patches by their manufacturers.
The cyber security industry has been aware of examples of these networks for some time and has publicly reported on the widespread scale of the threat and its implications. Mandiant Intelligence produced a public blog in May 2024 talking about covert networks in which they highlighted a key issue for defenders – indicator of compromise (IOC) Extinction. If a particular threat group could now come from one of many covert networks, each with potentially hundreds of thousands of endpoints, and each used by multiple threat actors, old network defence paradigms of static malicious IP block lists will be less effective. This is compounded by the dynamic nature of these networks where new nodes will be added as old devices are patched or removed from use.
Typical network topology
The number of covert networks used by China-nexus cyber actors is large, with new networks regularly developed and deployed. The existing covert networks change too, either because of defensive or legal action, or simply as a result of software updates and new exploits being used to target different technologies for incorporation into the network.
Because of this, a description of all known covert networks in detail, including how they are constructed and how they communicate, would immediately be out of date – and for most network defenders would not be practically useful.
However, most covert networks of compromised devices use the same basic set up. Understanding this generalised structure can aid researchers and defenders by helping them to understand which part of a network they may have found, and how to defend against it.
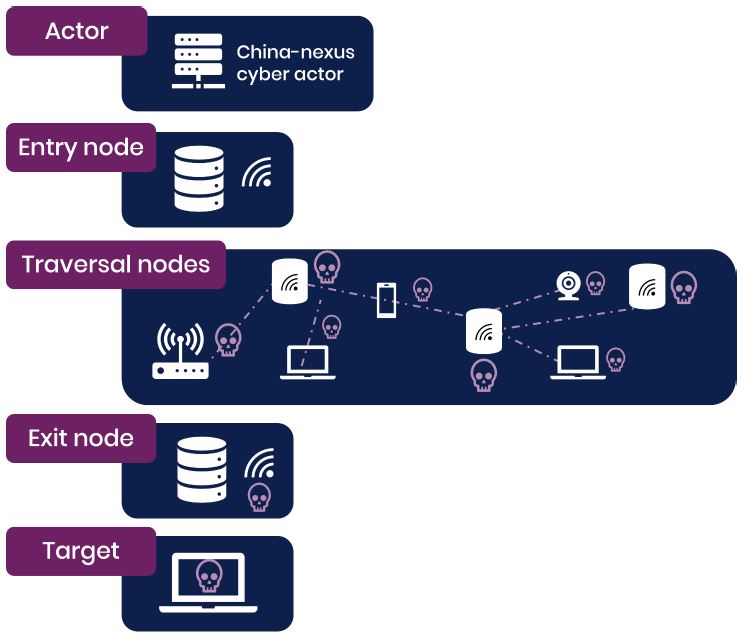
The diagram above illustrates the basic setup of a covert network, where typically an actor will connect to the network via an on-ramp or entry node. Their traffic will be forwarded through multiple compromised devices, used as traversal nodes, before exiting the network from an exit node, usually in the same geographic region as the target.
Protective advice
Defending from attackers using covert networks is not straightforward, and defensive tactics will be different based on the levels of resource and the nature of the target organisation. General advice for good cyber security practice should be followed, and some key messages can be found in the appendix of this advisory.
The following advice is specifically tailored to steps which can be taken to combat the risk of attacks coming from large, dynamic networks of compromised devices.
Further guidance for all organisations facing cyber security threats is available on the NCSC website.
This guidance should be considered alongside all applicable laws and regulations of the UK and co-sealing countries relating to the security of networks and data. It will be each organisation’s responsibility to ensure compliance with any such laws and regulations. Organisations should note that following the recommended actions set out below will not remove all risks.
All organisations
The NCSC recommends the following steps for all affected organisations to either take themselves, or ask their managed service and/or security providers to investigate for them:
- Map and understand network edge devices, developing a clear understanding of organisational assets and what should be connecting to them.
- Baseline normal connections, especially to corporate virtual private networks (VPNs) or other similar services.
- Would you expect connections from consumer broadband ranges?
- Leverage available dynamic threat feeds which include covert network infrastructure.
- Implement multi-factor authentication for remote connections.
Smaller organisations should consider creating and actioning a free NCSC Cyber Action Toolkit.
Larger or more at-risk organisations
Some more comprehensive measures may be appropriate if the risk to an organisation is high enough, to be conducted either in-house or through a security provider:
- Apply IP address allow lists rather than deny lists for connections to corporate VPNs for remote workers.
- Use geographic allow lists or profile incoming connections based on operating system, time zones, and/or organisation specific system configuration settings.
- Implement zero trust policies for connections.
- Enforce machine certificates for Secure Sockets Layer (SSL) connections.
- Reduce the internet-facing presence of the IT estate.
- Investigate machine learning techniques to profile normal network edge activity to detect and block anomalies.
The NCSC's Cyber Essentials can help protect organisations of all sizes.
Largest or most at-risk organisations
If Advanced Persistent Threat (APT) tracking is part of an organisation’s in-house capability, or if it is part of the service provided by a security vendor, consider tracking China-nexus covert networks as APTs in their own right.
- Active hunting – look for connections from IP addresses likely to be part of a covert network of compromised devices, for instance those hosting SOHO routers or IoT devices.
- Track and map covert networks reported by industry or government by looking at banners and certificates.
- Use threat reporting and threat feeds to create and implement dynamic blocklists and create alert rules to detect incoming threats.
- Consider using NetFlow feeds to look upstream and map covert networks to find new nodes.
The NCSC Cyber Assessment Framework provides guidance for organisations under the highest levels of threat, including those operating essential services, in sectors such as energy, healthcare, transport, digital infrastructure and government.
MITRE ATT&CK®
This advisory has been compiled with respect to the MITRE ATT&CK® framework, a globally accessible knowledge base of adversary tactics and techniques based on real-world observations.
| Tactic | ID | Technique | Procedure |
|---|---|---|---|
| Resource Development | T1584.005 | Compromise Infrastructure: Botnet | Botnets are used as core components of covert networks |
| Resource Development | T1584.008 | Compromise Infrastructure: Network Devices | Devices are compromised and added to botnets |
| Resource Development | T1583.003 | Acquire Infrastructure: Virtual Private Server | Virtual private servers (VPSs) are used in covert networks, typically as on-ramps |
| Command and Control | T1090.003 | Proxy: Multi-hop Proxy | Used by China-nexus cyber actors to route traffic |
